Knauf, As part of its commitment to a more sustainable and environmentally friendly future, it presented the results of the...
“One year as newlyweds + 18 years together as couples. A day I will never be able to forget.” With...
Bohemia Interactive's game will arrive on Steam in Early Access, and will be paid until version 1.0 is released Although...
The European Union President and the Italian Foreign Minister call for restraint after the Iranian attack European Commission President Ursula...
Puig will continue to grow through acquisitions. The Catalan perfume giant, which yesterday submitted its move to the stock market...
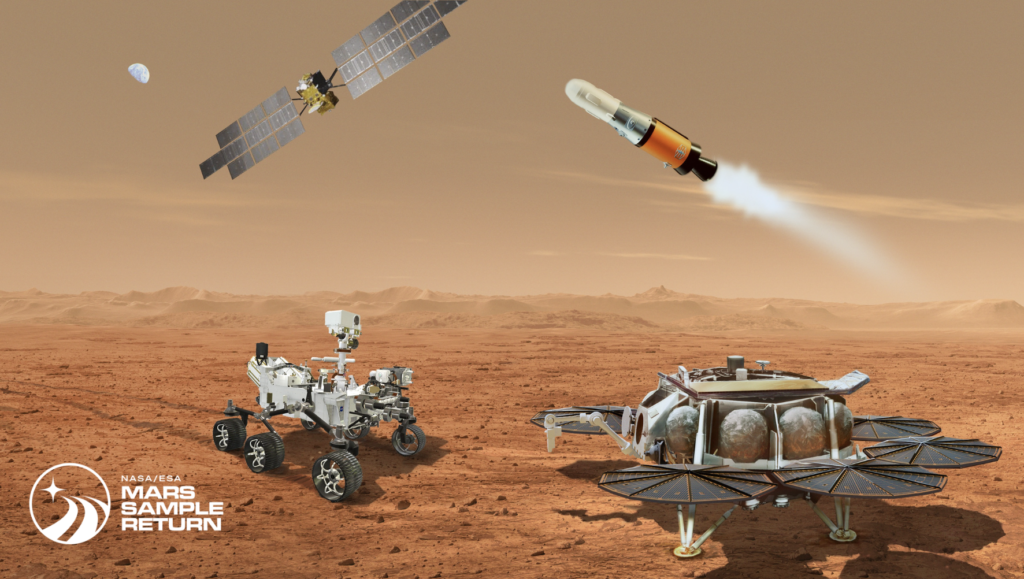
For several months, NASA's main planetary mission has been in jeopardy. Talking about the MSR program (Mars sample return), which...
In tennis, it meets in Madrid. This year the Mutua Madrid Open celebrates its 22nd birthday. Specifically, the best tennis...
"the Great Wall of China “It is the only human structure that can be seen from space.” For decades, this...
United State He objected to the decision on Thursday Security Council Subordinate United nations To grant full membership status to...
This translation device uses artificial intelligence to provide stability in simultaneous translation. In addition, it has 14 usage functions. (information)Although...








:quality(85)/cloudfront-us-east-1.images.arcpublishing.com/infobae/P7LSKWYROJABFFOOOKC2JQUNNQ.jpg)